Cloud security: Everything you need to know
As more businesses embrace the cloud, it’s vital that organizations don’t overlook security. In this article we will cover cloud security fundamentals and its importance in modern world.
What is cloud security?
Cloud security is a general term that covers a comprehensive set of policies, controls, procedures and technologies aimed to secure and protect cloud-based environments, applications, infrastructure and data stored in the cloud against malicious insiders and external threats.
As more companies move their digital footprint to the cloud, the need for cloud security systems continues to grow. Cloud is cheaper and more flexible, but consequently harder for traditional tools to maintain security.
Now let’s take a look at some most common and effective Cloud Security tools.
Cloud access security broker (CASB).
“Cloud access security brokers (CASBs) are on-premises or cloud-based security policy enforcement points placed between cloud service consumers and cloud service providers to combine and interject enterprise security policies as cloud-based resources are accessed,” according to Gartner.
If you need comprehensive visibility across multiple cloud environments as a business owner, cloud access security brokers can assist. CASBs inspect network traffic between the cloud provider and on-premises devices to ensure compliance with your security policies, all while managing and safeguarding the data you store in the cloud. When looking for a CASB tool, you should look for the following key features:
- Visibility – for example, shadow IT detection
- Compliance – e.g. user authentication and authorization
- Data security – which includes encryption and tokenization
- Threat protection – for instance, real-time malware detection
Cloud security posture management (CSPM).
IT professionals frequently use cloud security posture management (CPSM) solutions to detect compliance risks and misconfiguration issues in the cloud and to monitor an organization’s overall cloud posture. These solutions function by continuously assessing and identifying cloud assets and data across multiple clouds used by a company, including shadow IT. CSPM then generates a report that details any settings misconfigurations, allowing IT teams to address issues and improve the company’s overall cloud posture. These solutions will continue to monitor cloud environments in real time, highlighting internal and external issues and mistakes that may lead to additional vulnerabilities.
Cloud workload protection platform (CWPP).
Because cloud services are so simple to set up, many businesses make the mistake of overlooking critical security settings and configurations. However, with an ever-increasing range of threats such as denial of service attacks, data breaches, and phishing attacks, IT leaders must ensure that their workforce is protected at both the workload and endpoint levels. A cloud workload protection platform (CWPP) provides high-level visibility and allows for the monitoring of workload behaviour, as well as the detection and response to misconfiguration issues or intrusions. The gathered strategic data is presented in the form of a dashboard. By identifying outdated and weak business applications and user permissions settings, CWPP can also improve system hardening and overall vulnerability management.
Cloud security VS traditional security
In the cloud era, users can access apps from a variety of devices, including smartphones, tablets, laptops, and desktop computers. They also can access applications from any network, use public WiFi, and share files with multiple people, resulting in many privacy concerns that cloud security must address.
While on-premises security tools are frequently chosen by the business or IT provider, cloud security is typically a built-in partnership between the company and the cloud provider. Cloud security must be tailored to protect the business and create a manageable solution that is easy to monitor given the huge volumes of accesses and files involved, regardless of whether your cloud solutions are private, public, or hybrid, and depending on which cloud service your staff accesses.
The benefits of cloud computing security.
The advantages of cloud security are numerous, bringing all of the traditional cloud features as well as business-specific elements that make it easier and less expensive to customize for your needs.
1. Quick deployment
You acquire it, activate it, and tell it what to protect, as with most cloud services. In contrast, traditional security requires network hardware to be installed, security tools and patches to be applied across multiple machines, and complex rules and policies to be drafted, tested, and implemented.
2. AI adoption
Many cloud services use artificial intelligence to monitor events and can report abnormal activity faster than a traditional service that may require regular patching, firmware updates, and other complications. All updates happen instantly in the cloud, with only the occasional update causing outages across billions of operational instances per year.
3. Cost savings and reduced administration
The primary advantage of cloud security is the reduction in costs for dedicated hardware, applications, and the personnel required to run them. While many on-premises security tools are susceptible to failure, attacks, or outages, cloud users simply will not tolerate them, and tools reflect that urgent need. Furthermore, dashboards and alerting tools reduce IT professionals’ workload, allowing them to focus on operational issues.
4. Protection against DDoS attacks
A fixed point of attack is an on-premises server or database, whereas the cloud provides massive bandwidth and depth to protect against DDoS attacks, with cloud security tools rerouting traffic, providing backup resources, and other tricks to keep a business running during events that would cripple a traditional IT infrastructure.
How does cloud security work?
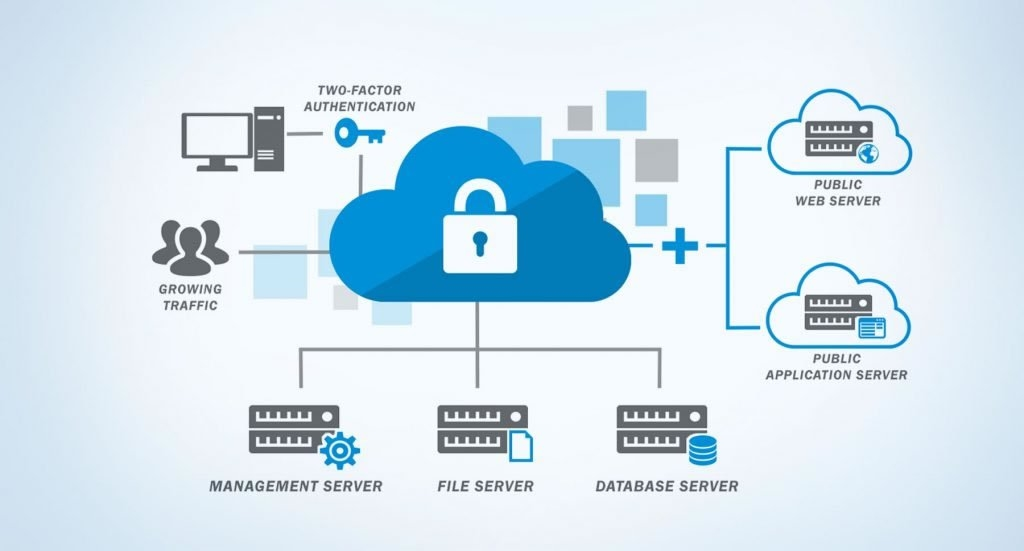
Native cloud security tools offer a variety of features that enable businesses to create cloud policies, manage data privacy, and identify security issues across their cloud footprint and IT assets. The importance of data protection and security remains paramount in the age of GDPR and other security regulations.
Cloud security helps by:
- Preventing unauthorized access to data stores
- Preventing users from sharing files they should not share
- Protecting against common internet attacks such as DDoS
- Enabling secure encryption between users and data
- Enabling compliance professionals to establish rules for any industry-specific protection.
Cloud security solutions provide tools such as cloud access security brokers, cloud inspectors, and cloud security controls to accomplish all of this. Analytics features such as user behaviour monitoring tools look for out-of-the-ordinary behaviour. This could be a user logging in from another country (after having their login information stolen) or multiple rapid sign-in attempts (suggesting someone is trying to brute force guess passwords).
Identity and access management, live threat intelligence, monitoring and prevention, cloud vulnerability and penetration testing, micro-segmentation, and smart firewalls are additional tools that work together to keep hackers out and your data safe. This combination provides a set of best practices, procedures, and guidelines that any business can use to defend itself.
Why you need a cloud security policy.
Every business requires a clear definition of what can and can’t be done in the cloud. Based on this, your IT department can select the best cloud security products and cloud services to create the most efficient, secure, and robust productivity tools.
The cloud is a friend to business, not a threat, and cloud security enables businesses to make the most of it while remaining secure. It only takes thought and understanding to provide a safe environment for your business to thrive.






